The Post-Quantum Wallet: Why Lattice-Based Security is the New Standard
Learn about how lattice-based cryptography, digital signatures and other quantum-resistant systems can be applied to protect wallets and blockchains for the post-quantum era.

The world of digital economy is on the verge of a major transformation as security models that have long been trusted are being questioned due to the emergence of quantum-safe cryptographic methods. While financial networks, identity management systems, and decentralised applications are growing around the world, their backbones, the encryption methods, are being forced to undergo an essential change. This shift is no longer theoretical; it is becoming an engineering reality.
Today, the urgency is clear: systems built for classical computing must evolve as the new benchmark in a rapidly advancing computational world.
The Rising Pressure on Modern Encryption
Most modern systems rely on cryptographic algorithms for the encryption of data, ensuring identity and sustaining trust. Nevertheless, new computational models can undermine these assumptions in many cases.
A public key is central to secure communication across wallets and platforms. However, as technologies progress, even the most common systems are susceptible to major security risks due to changing standards.
Developers are hence getting ready for a change in decentralized systems so that they can stay strong in the world that is going to be shaped by innovative computing power.
Why Classical Cryptography Is at Risk
One of the most significant threats comes from Shor’s algorithm, which can break widely used encryption systems. These are techniques that rely on public-key cryptography, the base of today’s digital security.
Because of Shor’s algorithm, attackers may implement the strategy of harvest now, decrypt later.
At the same time, computing capabilities continue to evolve, increasing the urgency for stronger adoption across global systems. This harvest now, decrypt later risk is why urgency is rising.
The Role of Digital Signatures in Security
Modern systems rely heavily on digital signatures to verify transactions, authenticate users, and ensure data integrity. These digital signature scheme models are essential for secure operations across financial platforms and decentralized environments.
However, emerging computational threats challenge the mathematical assumptions behind current systems. To counter this, new signature algorithms are being developed to meet next-generation security requirements, including hash-based signature scheme designs.
These next-generation approaches ensure authentication remains reliable even under advanced computational conditions.
Public Key Systems Under Pressure
Public key systems allow secure communication without exposing private credentials. They remain a foundational element of modern encryption.
However, increasing computational power puts these systems under significant pressure. Researchers are now exploring alternatives that strengthen encryption structures while maintaining usability across public key infrastructure.
Shor’s algorithm further highlights how fragile current systems could become, even enabling private-key recovery, pushing developers to build stronger frameworks for future infrastructure.
Lattice-Based Cryptography: The Future Foundation
The foundation of quantum-safe cryptography lies in lattice-based cryptography. Learning with Errors lies at the heart of one of its primary mathematical models. It is a model that continues to be secure, even if one takes into account the most advanced computational attacks.
These cryptographic algorithms are among those systems that are resistant to quantum computing and which have been designed to comply with the security standards.
Unlike traditional models, lattice-based models have been specifically engineered to resist the same level of classical threats as well as vehicles of future threats. This is essentially why they are the key in the field of modern cryptography.
System Integrity and Data Protection
Data integrity remains a core pillar of cybersecurity. While existing mechanisms are effective today, new computational models introduce challenges that require stronger designs and updated security constraints.
With algorithms like the Grover algorithm, the effective strength of current systems is reduced, requiring upgrades under new security models to withstand quantum computers.
These improvements ensure systems continue to support secure operations in future environments.
Decentralized Systems in a New Era
Encryption is the common function that both centralized and decentralized systems rely on for their secure operation. Yet, emerging computational threats pose a challenge that can only be met by the introduction of quantum-safe cryptography.
To adapt, modern platforms are integrating quantum-resistant structures aligned with future-ready security principles. The idea of smart contracts is also being re-evaluated in secure execution environments.
Transitioning to Quantum-Resistant Systems
Quantum-resistant algorithms make a transition that is critical for cybersecurity that lasts. They have security features that enable them to be safe even in the presence of highly advanced computational resources.
Current cryptographic algorithms are being redesigned to ensure compatibility with both present and future threats under Post-Quantum Encryption Standards. Some platforms are also experimenting with hybrid protocols to bridge classical and quantum-safe approaches. In some cases, some new architectures like lattice-based and code-based cryptography are completely replacing the old ones.
Such a move guarantees that the system will stay stable over time, even though technology may keep changing.
The Role of Digital Signatures in Post-Quantum Systems
Digital signatures will have to change quite a bit in the post-quantum world. Existing ones rely on mathematical assumptions that might be undermined in the new world that is being foreseen. Different kinds of systems are under experimentation by the researchers to stay one step ahead of the quantum computations, e.g. lattice-based cryptography, hash-based cryptography, and post-quantum cryptographic signatures.
As a result, new lattice-based signature models are being introduced alongside hash-based signature scheme approaches. These ensure secure authentication even when traditional assumptions fail.
At the same time, supporting mechanisms continue to maintain data integrity across transactions.
Public Key Evolution and Cryptographic Shifts
The evolution of encryption systems is central to next-generation cryptography. With increasing computational power, these systems are being redesigned to reduce vulnerabilities.
In parallel, traditional cryptography is being upgraded to support quantum-resilient frameworks.
This transformation ensures that identity verification and secure communication, such as the TLS handshake, remain reliable in future environments.
Elliptic Curve Cryptography and Its Limitations
One widely used system today is Elliptic Curve Cryptography (ECC), often implemented through the Elliptic Curve Digital Signature Algorithm, which provides strong security under classical assumptions.
This limitation is driving the shift toward alternative systems that can withstand next-generation attacks.
Grover’s Algorithm and Security Implications
The Grover algorithm plays a dual role in modern cryptography. While it enhances search efficiency, it also reduces the effective strength of security systems.
Because of this, current designs must be strengthened to maintain resistance against future threats.
Developers are already adjusting system parameters to account for these risks.
Post-Quantum Wallet Architecture
The post-quantum wallet represents the next generation of secure digital storage. It integrates lattice-based cryptography, stronger authentication systems, and advanced cryptographic designs built for resilience.
These wallets rely on improved verification systems, secure key structures, and modern encryption approaches like homomorphic encryption to ensure safety in a rapidly evolving environment shaped by quantum computers.
Additional Layer: Preparing for Quantum Disruption
Security discussions are intensifying, and quantum computing is moving from the realm of theory to the forefront of developers’ considerations for their security strategies. Quantum computers are not just threatened by speed; their main weapon is that they can handle problem-solving at a level that was deemed impossible before. Besides technology, this transformation also lies in a complete reevaluation of the laws of nature, where quantum physics is constantly discovering new dimensions of computation and security.
This is exactly the point when Shor’s algorithm becomes relevant. By targeting widely used encryption methods, Shor’s algorithm exposes why current systems cannot be relied on forever. The growing awareness around the Shor algorithm is pushing organizations to rethink their entire security stack, including hardware-supported trust anchors.
Rethinking Security Foundations
To adapt, experts are reconsidering the role that cryptographic primitives play, the cryptographic primitives are the fundamental building blocks of all secure systems.
If these cryptographic primitives turned out to be non-quantum resistant, all the work built on top of them would become vulnerable to quantum computers. Work on global standardization starting from the National Institute of Standards and Technology, is thus very important.
For everyday users, this effort means more than just technical compliance , it’s about trust. When standards are unified and transparent, people can feel confident that the wallets, apps, and platforms they rely on are built on foundations strong enough to withstand the quantum era.
Their work will not only ensure that future systems are secure but also globally uniform and trustworthy according to standards like FIPS 203 and FIPS 204.
Strengthening Data Integrity
Another critical area of focus is hash functions, which are widely used for verification and data integrity. While current hash functions are still effective, Grover’s algorithm introduces a new layer of risk by reducing their strength.
Because of Grover’s algorithm, programmers are not only rewriting hash functions but also exploring Verifiable Secret Sharing to maintain security over a long period. These must be the changes if we want to preserve the level of trust in today’s systems.
Emerging Technologies and Privacy
One of the most exciting developments in this space is Fully Homomorphic Encryption, which allows computations to be performed directly on encrypted data. This means sensitive information never needs to be exposed during processing.
As adoption grows, Fully Homomorphic Encryption could become a key component in secure systems, especially when combined with quantum-safe cryptographic designs, especially when combined with quantum-safe cryptographic designs and homomorphic encryption.
Impact on Decentralized Ecosystems
The development of security measures has a very significant influence on blockchain networks, since such networks largely rely on cryptographic trust and smart contracts.
As risks are increasing, blockchain networks must adopt quantum-resistant measures, including lattice-based cryptography and homomorphic encryption, which are capable solutions for securing and scaling the systems against quantum computers in the future.
Quecko: Building Quantum‑Safe Blockchain Systems
Quecko is known for solving the toughest problems in blockchain security. By focusing heavily on cryptography infrastructures and quantum-safe approaches as well as taking some risks, Quecko is making Web3 platforms ready for a time when quantum computers could break today’s encryption.
Quecko’s strategy is more than just making their defenses tougher, they are also figuring out what new threats could come up next. The developers are mixing hands-on methods with research that thinks ahead. As a result, the blockchain solutions they develop not only seem like they can handle the future but also remain user-friendly for people.
Its focus on hybrid protocols and advanced signature schemes is showing how the blockchain ecosystem can evolve to maintain security even under post-quantum conditions.
Conclusion
The rise of advanced computing is fundamentally reshaping cybersecurity. From authentication systems and encryption frameworks to smart contracts, all layers are experiencing significant changes.
Traditional cryptographic algorithms are no longer sufficient on their own, especially with threats like Shor’s algorithm, Grover’s algorithm, and quantum computers challenging existing models.
By applying lattice-based schemes, enhancing the safety and integrity of the system, making use of homomorphic encryption, and moving to quantum-safe cryptography, the sector is laying down a strong and secure basis for the future.
The post-quantum wallet is not just an upgrade—Post-quantum wallets will not be a mere update but rather the next crucial stage in securing digital assets in a world of fast-changing and advanced technology.
FAQs
1. Why is everyone talking about lattice-based cryptography now?
Because it’s one of the few approaches that can actually hold up against quantum computers. Instead of relying on old math problems, it uses structures that are much harder to break, even for future machines.
2. Are blockchain networks really at risk from quantum tech?
Not immediately, but it’s something they can’t ignore. Many blockchain networks are already working on upgrades using stronger cryptographic primitives and smart contracts, so they’re not caught off guard later.
3. Do hash functions stop working in the future?
They don’t cease to work, but they do get weaker. With Grover’s algorithm, the hacker will be able to do the search pretty fast so changing the hash functions to be much stronger is going to be crucial for the safety to remain intact.
4.How is Quecko connected to post‑quantum security?
Quecko specializes in blockchain systems that rely on advanced cryptography. As quantum computers grow more powerful, Quecko’s focus on lattice‑based security, hybrid protocols, and post‑quantum cryptographic signatures ensures that decentralized platforms can remain safe and scalable in the long run.
5. When will we actually see quantum-safe security everywhere?
It’s already starting. Big efforts led by groups like the National Institute of Standards and Technology are pushing companies to adopt safer systems step by step through NIST standardization..
Date
2 hours agoShare on
Related Blogs

The Post-Quantum Wallet: Why Lattice-Based Security is the New Standard
2 hours ago
Bitcoin Above $73,000 Despite a Global War: Is Crypto Becoming the New Safe Haven?
2 hours ago
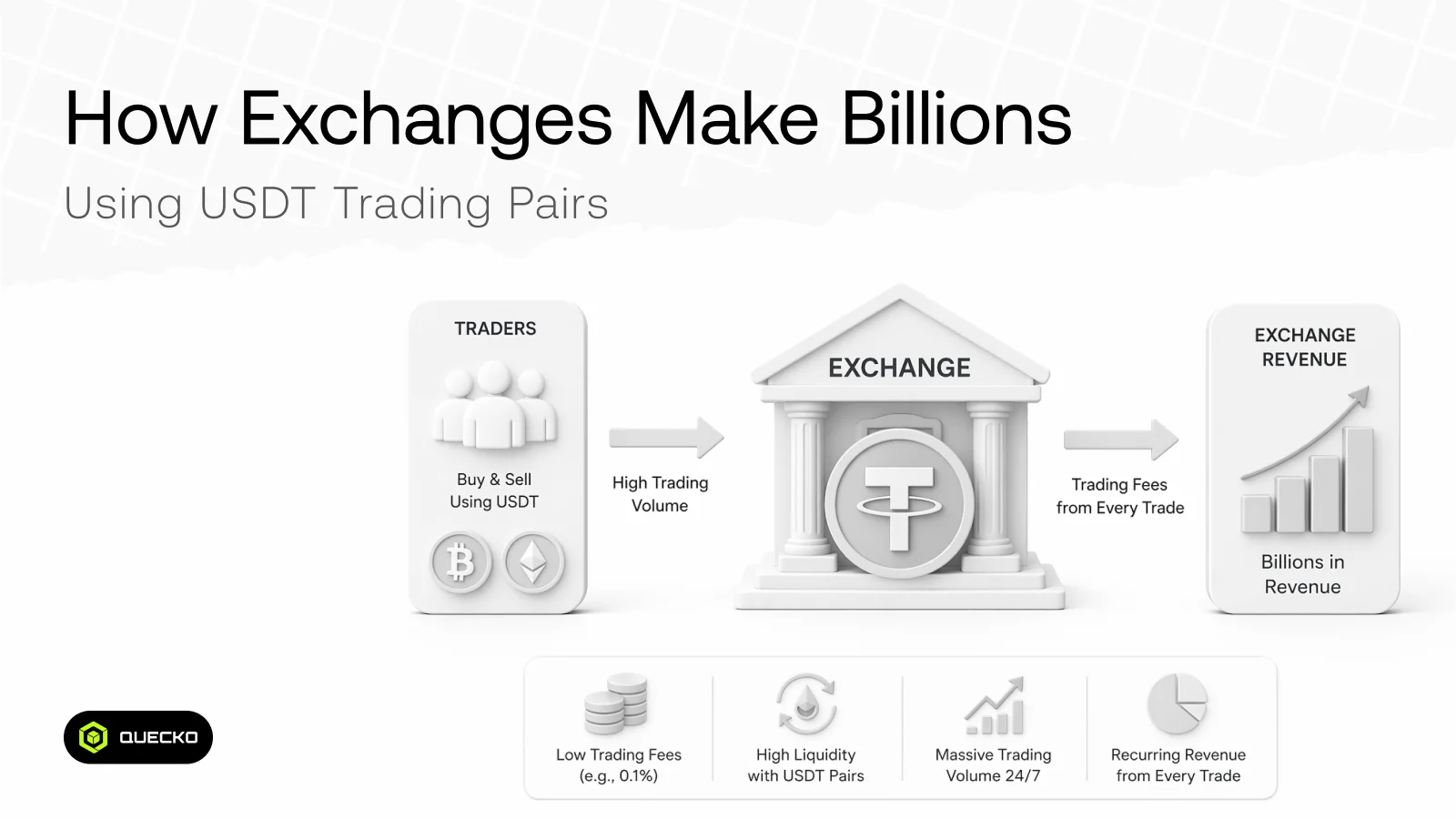
How Exchanges Make Billions Using USDT Trading Pairs
3 days ago
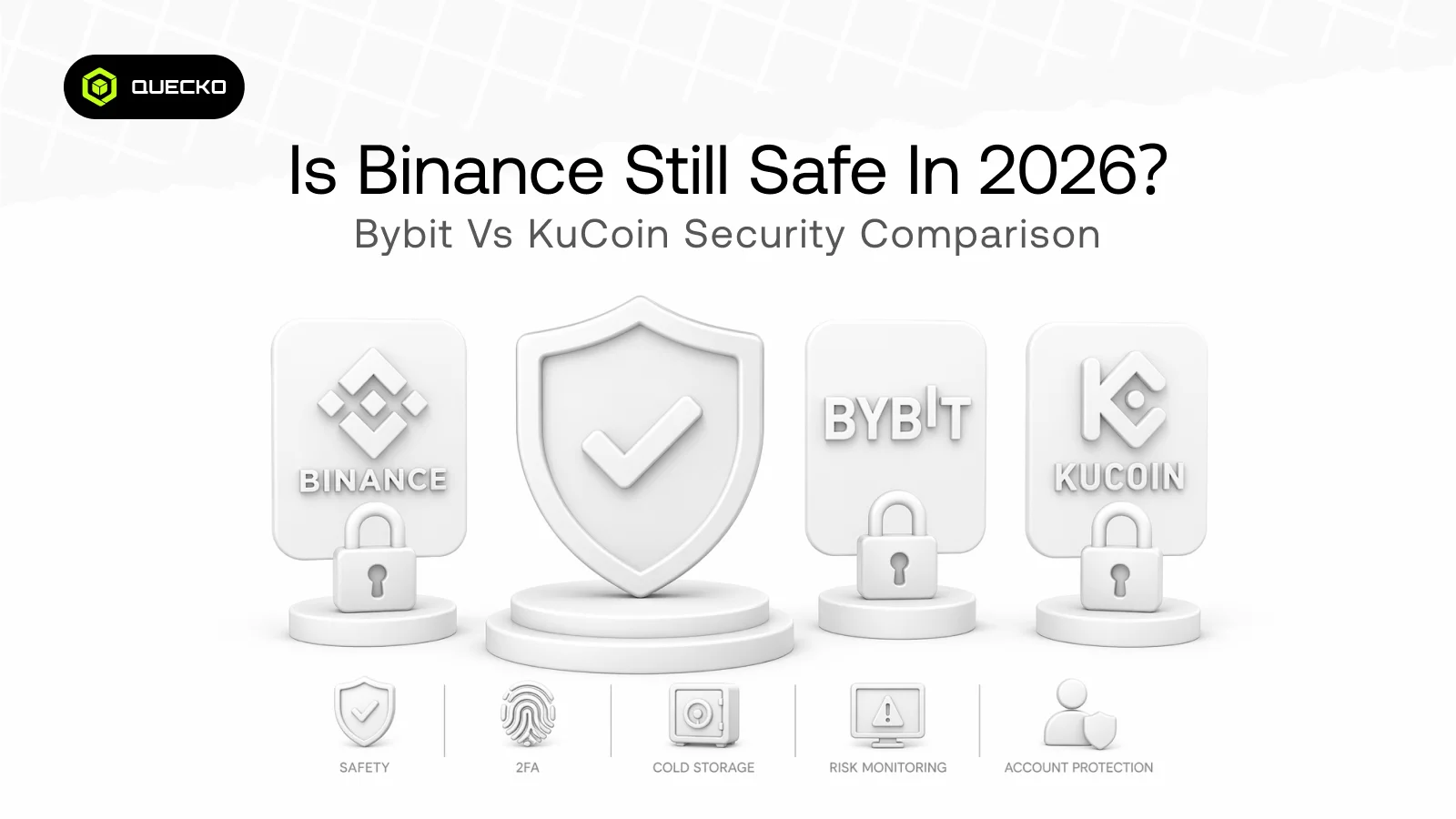
Is Binance Still Safe in 2026? Bybit vs KuCoin Security Comparison
3 days ago